AWS:
Amazon Web Services is one of the most popular Cloud Provider that has free tier too for students and Cloud enthutiasts for their Handson while learning (Create your free account today to explore more on it).
Read from here
User Data in AWS:
When you launch an instance in Amazon EC2, you have the option of passing user data to the instance that can be used to perform common automated configuration tasks and even run scripts after the instance starts. You can pass two types of user data to Amazon EC2: shell scripts and cloud-init directives.
You can also pass this data into the launch instance wizard as plain text, as a file (this is useful for launching instances using the command line tools), or as base64-encoded text (for API calls).
This will save time and manual effort everytime you launch an instance and want to install any application on it like apache, docker, Jenkins etc
Read more from here
IAM:

here are the key points about IAM:
IAM is a service provided by AWS (Amazon Web Services) for managing user identities and access to AWS resources.
IAM enables you to create and manage AWS users and groups, and control their access to AWS resources.
IAM allows you to assign policies to users and groups to control their permissions for accessing AWS resources.
IAM provides features such as multi-factor authentication (MFA) for increased security.
IAM is a fundamental component of AWS security and helps you ensure that only authorized individuals and services can access your AWS resources.
Task1:
Launch EC2 instance with already installed Jenkins on it. Once server shows up in console, hit the IP address in browser and you Jenkins page should be visible.
Take screenshot of Userdata and Jenkins page, this will verify the task completion.
steps
Open the AWS Management Console and go to the EC2 Dashboard and Click the "Launch Instance" button.

Choose an Amazon Machine Image (AMI) that has Jenkins pre-installed. For example, you can choose the "Ubuntu Server 20.04 LTS (HVM), SSD Volume Type" AMI provided by AWS and select the "Jenkins" option under the "Choose an Instance Type" section.

Configure the instance details, such as the instance type, VPC, and subnet.

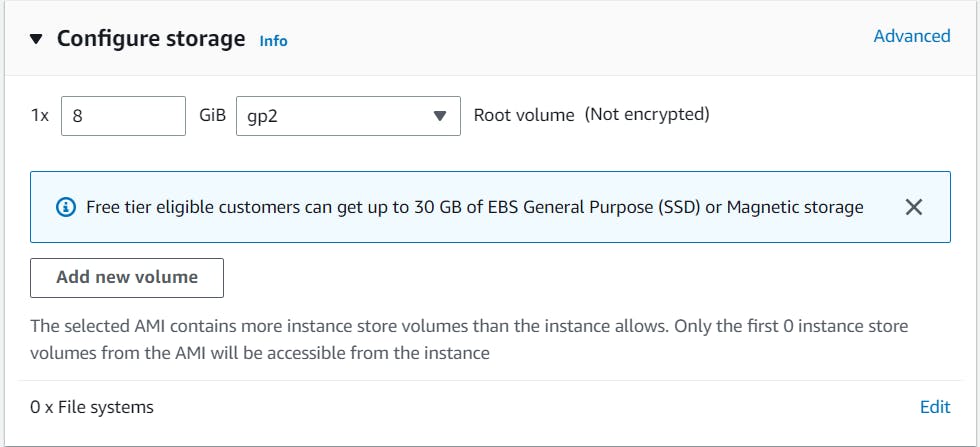
Add storage to the instance if needed.
Configure security groups to allow inbound traffic to port 8080 (the default Jenkins port).

In the "Advanced Details" section, add the User Data script to install Jenkins on the instance during launch. The User Data script can include commands to install Jenkins and any required dependencies. and Review the instance details and launch the instance.

Once the instance is launched, wait for it to show up in the EC2 console and note down its public IP address.

Open a web browser and enter the public IP address followed by ":8080" (e.g., http://<public_ip_address>:8080).

Task2:
Read more on IAM Roles and explain the IAM Users, Groups and Roles in your own terms.
IAM (Identity and Access Management) is an AWS service that allows you to manage users, groups, and roles in your AWS environment. These three components work together to provide granular access control and permissions for your AWS resources.
IAM Users: IAM users are individual AWS accounts that you create for the people or applications that require access to your AWS resources. Each user has a unique set of security credentials, including a user name and password, access keys, and permissions. You can create, modify, and delete users as needed, and grant them specific permissions to access or manage AWS resources.
IAM Groups: IAM groups are collections of IAM users. You can use groups to simplify permissions management, by assigning permissions to a group instead of individual users. For example, you can create a group for developers and assign permissions to access development resources. When you add a user to the group, they automatically inherit the group's permissions.
IAM Roles: IAM roles are another way to manage access to AWS resources. Roles are similar to users, but they are not associated with a specific person or account. Instead, roles are assumed by trusted entities, such as EC2 instances, Lambda functions, or other AWS services. Roles can have permissions policies attached to them, which define the specific permissions that the role is allowed to use.
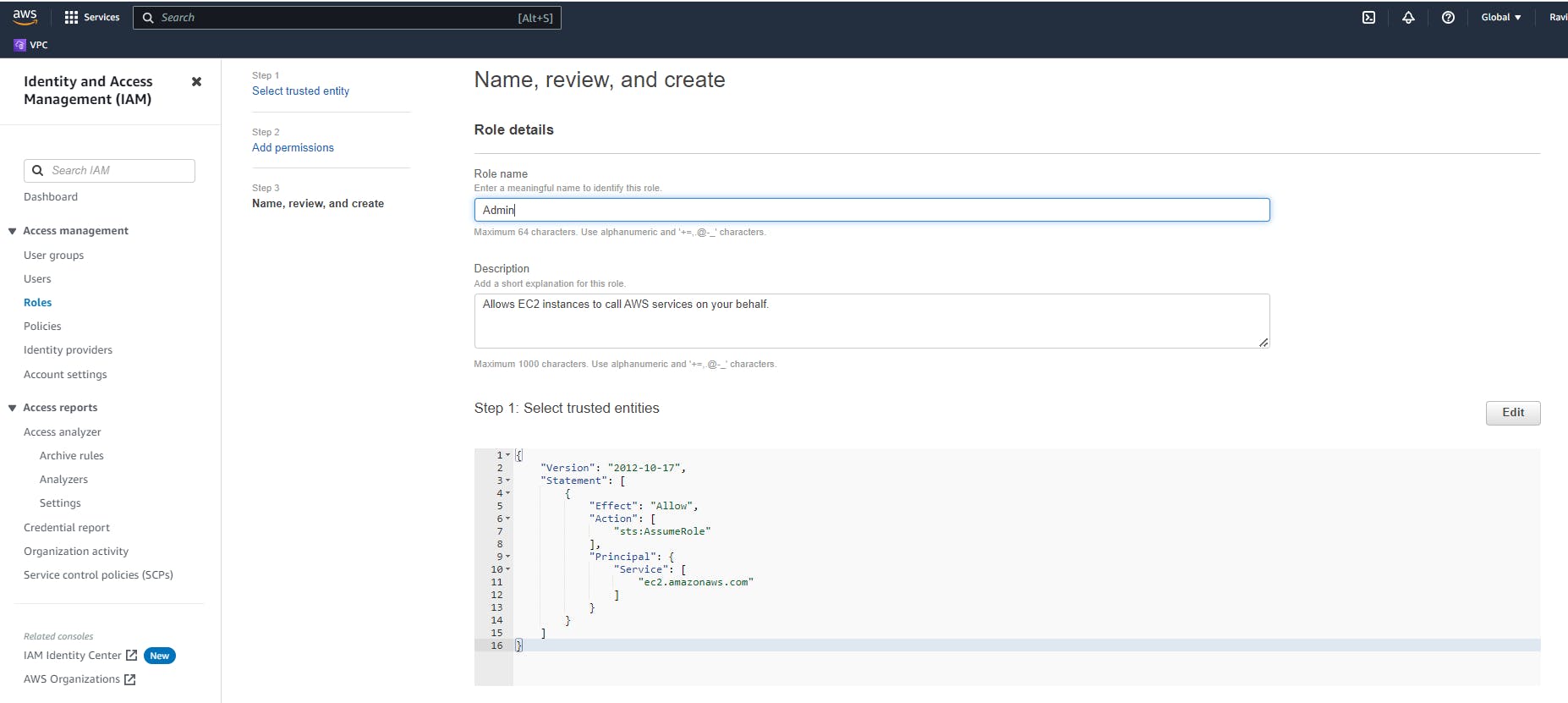
Create three Roles named: DevOps-User, Test-User and Admin.
Log in to the AWS Management Console and navigate to the IAM dashboard.
Click on "Roles" in the left-hand menu and then click on the "Create role" button.

Choose the appropriate use case for the role. For example, if you want to create a role for an EC2 instance, choose "AWS service" and then "EC2".

Select the appropriate permissions policies for the role. You can choose from existing policies or create a custom policy.

Enter a name for the role and click "Create role".

Repeat the above steps for each role you want to create: DevOps-User, Test-User, and Admin.
Create a Test-User role

Create a Admin role

Once the roles are created, you can assign them to individual IAM users or groups as needed, and control their access to AWS resources.
Thank you for reading!
